Yi IoT Home Camera Riddled with Code-Execution Vulnerabilities
Por un escritor de hombre misterioso
Descripción
Five of them allow remote compromise of the IoT gadgets, so attackers can intercept video feeds and more.

Warning: New Malware Emerges in Attacks Exploiting Ivanti VPN Vulnerabilities

DJI Archives – Unmanned Aerial Vehicle
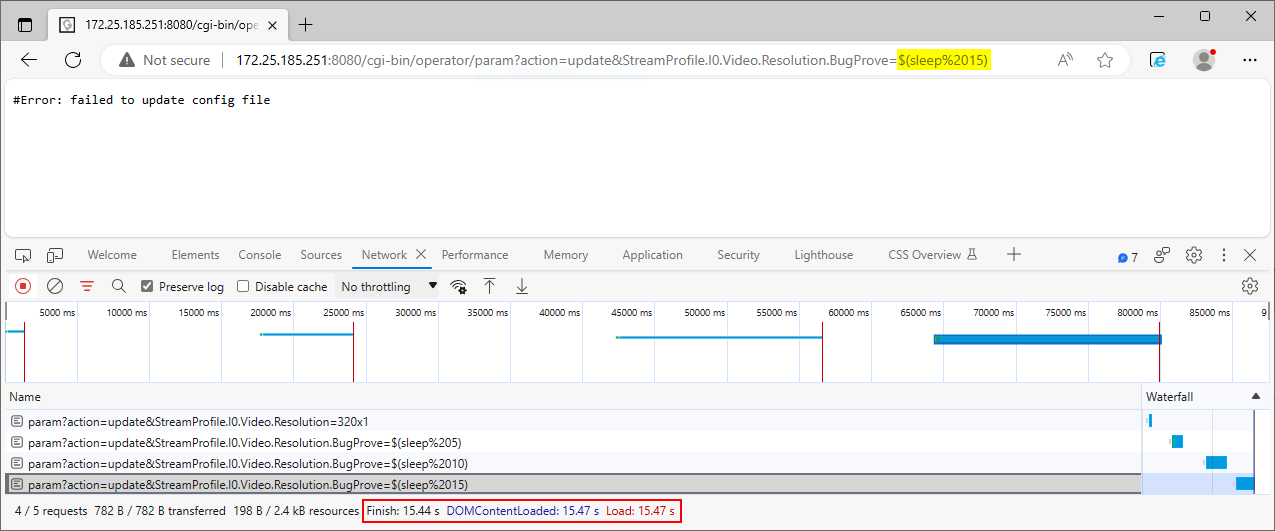
IoT Bug Hunting - Part 2 - Walkthrough of discovering command injections in firmware binaries

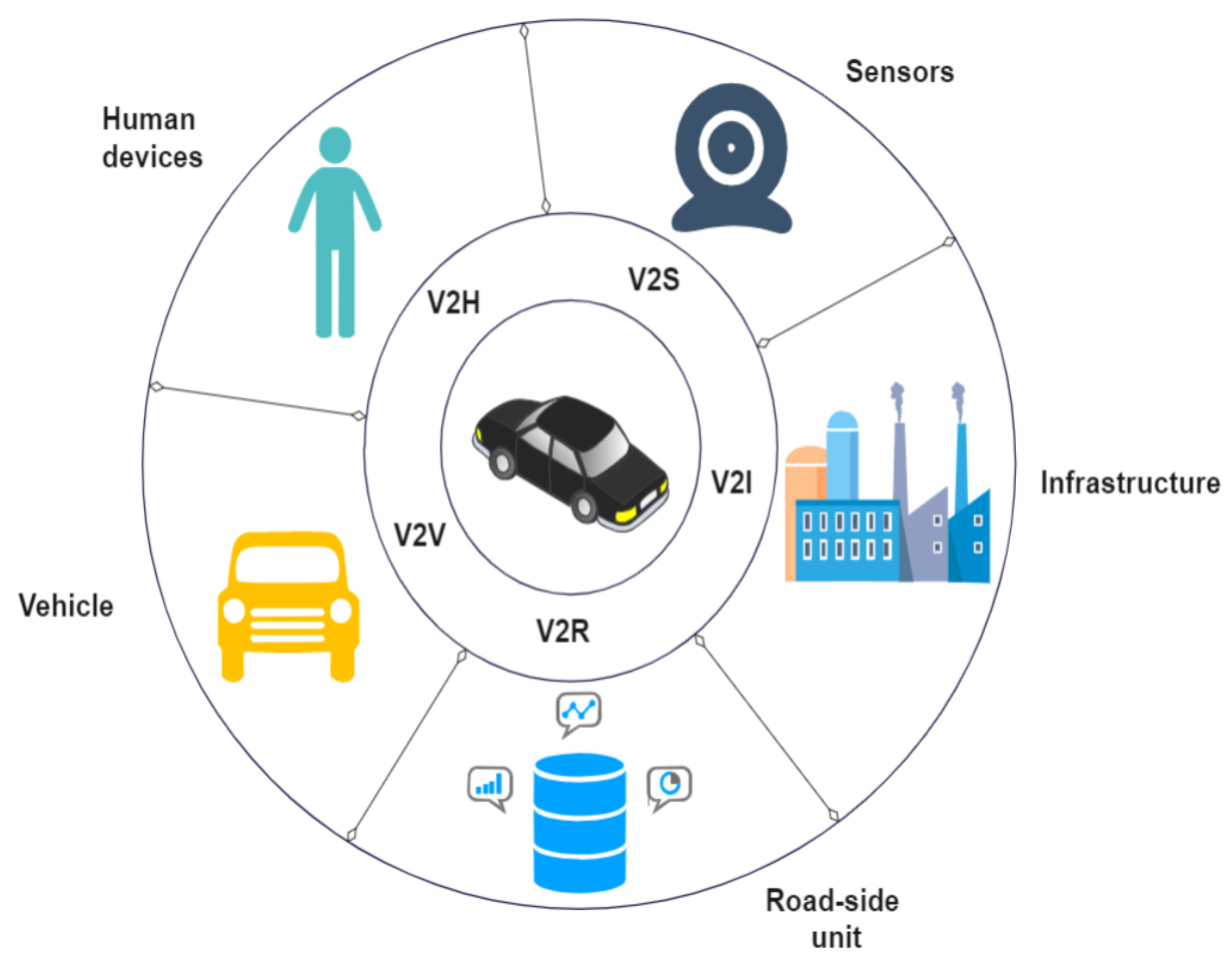
Inquiring Into Security Requirements of Remote Code Execution for IoT Devices

Simple Remote Code Execution Vulnerability Examples for Beginners, by Ozgur Alp

A Review on the Security of the Internet of Things: Challenges and Solutions

Fog computing for next-generation Internet of Things: Fundamental, state-of-the-art and research challenges - ScienceDirect
Sensors, Free Full-Text

EECS A Year in Review Magazine 2017 by Electrical & Computer Engineering at University of Michigan - Issuu
PDF) Analysis of Consumer IoT Device Vulnerability Quantification Frameworks

A systematic review of the purposes of Blockchain and fog computing integration: classification and open issues, Journal of Cloud Computing
PDF) Machine and Deep Learning for IoT Security and Privacy: Applications, Challenges, and Future Directions

Zero Day Initiative — Riding the InfoRail to Exploit Ivanti Avalanche
de
por adulto (el precio varía según el tamaño del grupo)







